Digital Marketing and Third Party Data Breaches
Businesses often outsource and collect data from third parties to plan effective marketing strategies and increase the relevancy of their ad campaigns. These third-party vendors can traverse business firewalls and acquire resources attached to the vendor segment. They are the primary source that collects user data and processes it to the service providers. On both ends, these vendors have the authority to access sensitive information. From a marketing perspective, outsourcing data collection to third-party vendors increases personalisation and efficiency. However, this third-party data collection is gradually emerging to be the greatest threat to data security.
 Digital Marketing and Third Party Data BreachesIn a recent interview Jose Granado, a CISSP-certified personnel expressed his concerns about the increasing third-party data breaches. His primary concern lies with the business’s incumbent third party related security management. This interview with the IT world exposed how big companies like Twitter, Facebook, etc are vulnerable to the increasing threat of data breaches.
Digital Marketing and Third Party Data BreachesIn a recent interview Jose Granado, a CISSP-certified personnel expressed his concerns about the increasing third-party data breaches. His primary concern lies with the business’s incumbent third party related security management. This interview with the IT world exposed how big companies like Twitter, Facebook, etc are vulnerable to the increasing threat of data breaches.
The Use of Third Party Vendors
The global pandemic has changed the entire scenario of digital marketing. While some businesses have perished due to a lack of sustainable marketing strategies, most of them have upscaled themselves by shifting their bases online. This transition has compelled the personalisation of ad campaigns to ensure brand relevancy amongst consumers. According to the Pew Research Center, 77 per cent of consumers in the U.S. own a smartphone. Thus it is crucial to send the right message to the right consumer through the platform on which they devote maximum time of their daily lives.
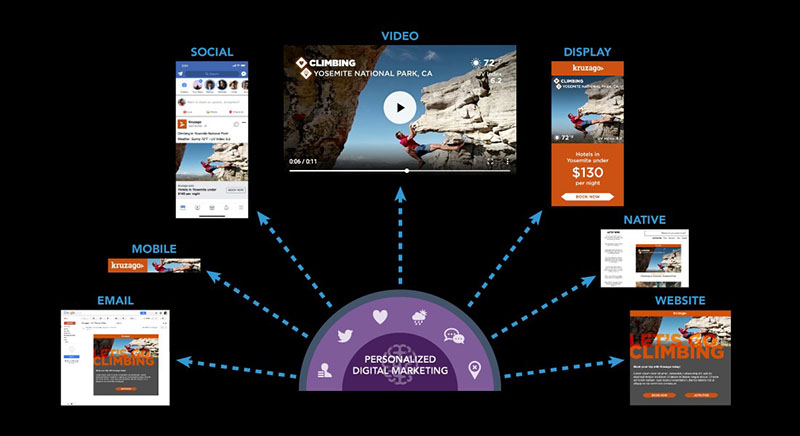
Considering the benefits, businesses use Data Management Platforms (DMPs) or data providers to track user web browsing activities. These platforms mainly use website cookies, social media networks, surveys, and forms to obtain the user browsing history. Breaking down those insights provides clarity about the preferences and requirements of their users. It allows them to choose the best platform for their brand, which can help them to reach out to their target audience. Using these insights, marketers create personalised ad campaigns, sales copies, or landing pages to appeal to the users who are either interested or require their services.
Third Party Sources and Their Security Concerns
According to the research conducted by Securelink and Ponemon Institute, almost 44 % of the business have experienced third-party data breaches in the past 12 months. This report demonstrated that the data attacks are occurring due to their lack of security and data management measures.
Per the report, the following are the prime reasons responsible for the severe data risks-
- Not Prioritising Security Checks- More than half of the businesses do not access the security measures and credibility of the third-party vendors before outsourcing their services.
- Excessive Reliance on Reputation- 63% of the respondents have blamed the brands for relying excessively on reputation. As a result, most brands fail to access and define the various stages of security threats.
- Lack of Monitoring- Businesses outsource data collection to third-party vendors for tracking their audience web browsing activity. However, most of them have minimal or no tracking methods to monitor the activities of thee third-party vendors. It is a severe security threat to their sensitive information.
- Unlimited Access to Third-party Resources- To increase the personalisation of marketing campaigns, businesses give third-party vendors the access to traverse primary firewalls. 51% of the respondents consider the lack of centralised control over this access to be responsible for the data breaches.
How Can Businesses Prevent Data Breaches?
The lack of accountability of business is often the prime reason for the majority of data breaches. According to the experts, organisations should employ competent security measures. Taking such security measures for granted can cause severe harm to both businesses and their consumers.
Google’s recent migration to Floc in Q2 of 2021 has initiated a shift to further first-party-oriented marketing campaigns. This transition has created a whirlwind in the marketing realm. Industry experts have considered this landmark migration to be the first initiative towards building breach immune services. Utilising this change businesses can undertake the following measures to protect their sensitive data from third-party breaches –
- Focusing on the first party-oriented data collection- Instead of outsourcing data collection to third-party vendors, businesses need to employ first party-oriented data collection methods. They need to discard data collection through social media networks, surveys, forms, and advertisements. Instead, they should shift their focus to other methods like-gating website entry by user registration forms.
- Behavioural Targeting – third-party tracking of data is a generic way to map the browsing activity of the target audience. Whereas people-based targeting is the most effective way to target and obtain information about leads who are interested in availing their services. Employing this method will involve contextual advertisement, in which the ads displayed on websites will be relevant to the website content.
Employing first-party-oriented marketing strategies will help businesses to foster a holistic relationship with their consumers. At the same time, it will help them to develop security management to protect them from data breaches.
Conclusion
Various studies have shown how a lack of control and knowledge of third-party access can result in severe security threats. Thus, business needs to stop taking security management for granted and build efficient centralised security models. Along with upscaling their marketing campaigns, they need to focus on data management and assessment of the third-party segments. To conclude, considering the increasing threat of breaches, it’s a prerequisite for a business to develop more centralised control over third-party access.
References:
- https://www.computerworld.com/article/2817626/most-organizations-fail-to-manage-risks-associated-with-sharing-data-with-third-parties.html
- https://www.upguard.com/blog/biggest-data-breaches
- https://www.techradar.com/in/news/over-half-of-organizations-have-experienced-a-third-party-data-breach
- https://www2.deloitte.com/ng/en/pages/governance-risk-and-compliance/articles/third-party-risk.html
Written by The Original PC Doctor on 18/06/2021.