Cryptolocker Virus Definition
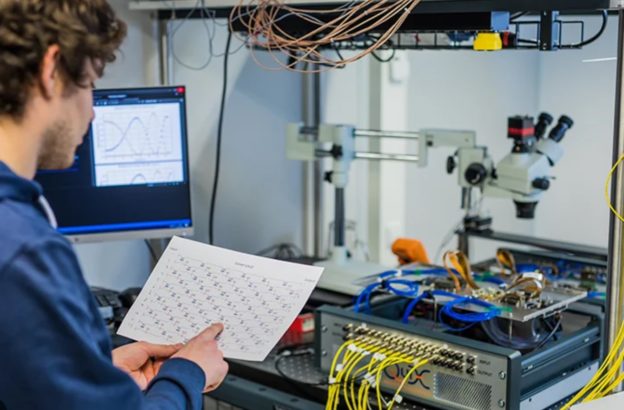
If you are conversant with the technological terminologies, the term Cryptolocker is not a surprise. It is a virus that attacks and cripples your files. This Trojan horse malware is discreet, and often, you will never notice until all your files are encrypted. Once it gains access into your network, it attacks almost everything from your desktop, laptop, and all shared network files. This includes the memory cards, and USB memory drives. The target victims are usually large data processing organizations.
Furthermore, the Trojan virus singles out the Windows operating system. If you are on a Macs system, you are slightly safe for now. In ensuring stealth in its operation, the hackers gain access to the security wall of your network. Then the virus locks the files that can be encrypted. The asymmetric encryption then disables your data through a public key. Upon completion, the hackers demand a ransom to decrypt the coding through a private key. Similarly, the Trojan virus keeps sending warning reminders of a possible loss of files if you delay in buying the private key from the hackers.
Breaching the Security Walls
Surprisingly, the hackers can easily pass your security wall through emails, attachment downloads, and files sharing sites. Again, you can fall victim to a Cryptolocker attack through videos and other plug-ins from unsecured websites or blogs. The files in email attachments appear as regular files. For instance, they may be doc or pdf. Unknown to you, they do have an extension.
Once you open the files, the Trojan virus downloads in your drive. When this is happening, your computer goes on with its normal operations. You can only discover when your files are locked and encrypted. After the mission is through, hackers send in reminders of deleting your data if you do not pay up for the key. Most of the reminders have a countdown clock for the warning.
Precautions
Ideally, you can remove the Trojan virus from your computer system with many antivirus programs available. The catch here is, only the private key can decrypt the files. In the long run, most people resort to a more natural way out. They pay up the ransom for the private key. Once the data is decrypted, they scan and delete the malware.
In protecting your computer network from hackers, you are the first line of defence. Yes, you may be getting a lot of traffic in your email. If you do not have a secure security wall, do not open email attachments from doubtful sources. This includes your unfamiliar blogs, websites, or financial institutions. It is good to second confirm an email by calling the source if you were not expecting anything.
Again, scan all the emails and attachments that you get before opening them. The Rescue Utility Disk is the best option for starters. It helps you to copy data to a USB drive or other storage outside the shared drive. In case of any malfunctioning, you can still reboot your system through your external media. By doing this, you sanitize the computer of any virus.
Cryptolocker is a nightmare for any precious data you have. It is prudent to have reliable backup files. Finally, invest in a powerful scanning system to minimize the risks of any attacks.
Written by The Original PC Doctor on 11/02/2020.